Vortex Threat Intelligence
Our patented global threat cloud processes millions of IOCs daily, delivering actionable intelligence that powers the entire Beacon Technology ecosystem.
Our patented global threat cloud processes millions of IOCs daily, delivering actionable intelligence that powers the entire Beacon Technology ecosystem.
Millions of Indicators of Compromise processed daily from global sources, delivered to your security stack in real-time.
Intelligence aggregated from commercial feeds, open-source intelligence, dark web monitoring, and proprietary research.
Every IOC enriched with threat actor attribution, campaign context, MITRE ATT&CK mapping, and confidence scoring.
RESTful API for seamless integration with SIEM, SOAR, EDR, and firewall platforms. STIX/TAXII support included.
Historical lookback capabilities and hunting queries to identify past compromises using newly discovered IOCs.
Automated deduplication and validation to reduce false positives and alert fatigue in your security operations.
Vortex aggregates and normalizes threat intelligence across all major indicator types, providing complete coverage for your security operations.
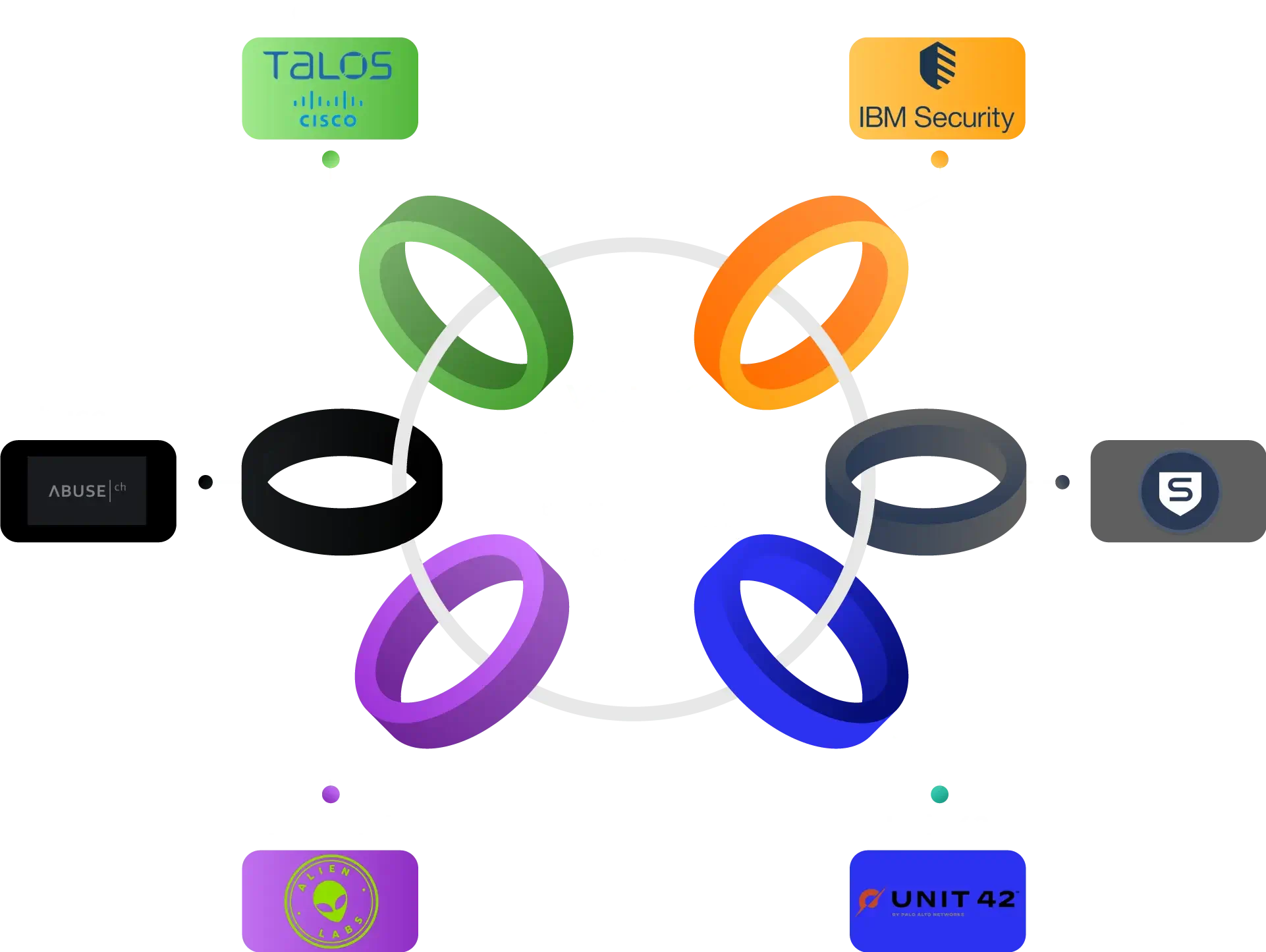
Vortex integrates with your existing security stack through industry-standard protocols and native connectors.
Contact us to learn how Vortex threat intelligence can enhance your security operations.
Request Integration Guide