Compliance as a Byproduct of Real Security
The CYFAX Compliance Cockpit is not a GRC checkbox tool. It is a regulatory crosswalk engine powered by actual cybersecurity operations. The compliance evidence it produces is real because the threat intelligence, dark web monitoring, control validation, and network detection behind it are real.
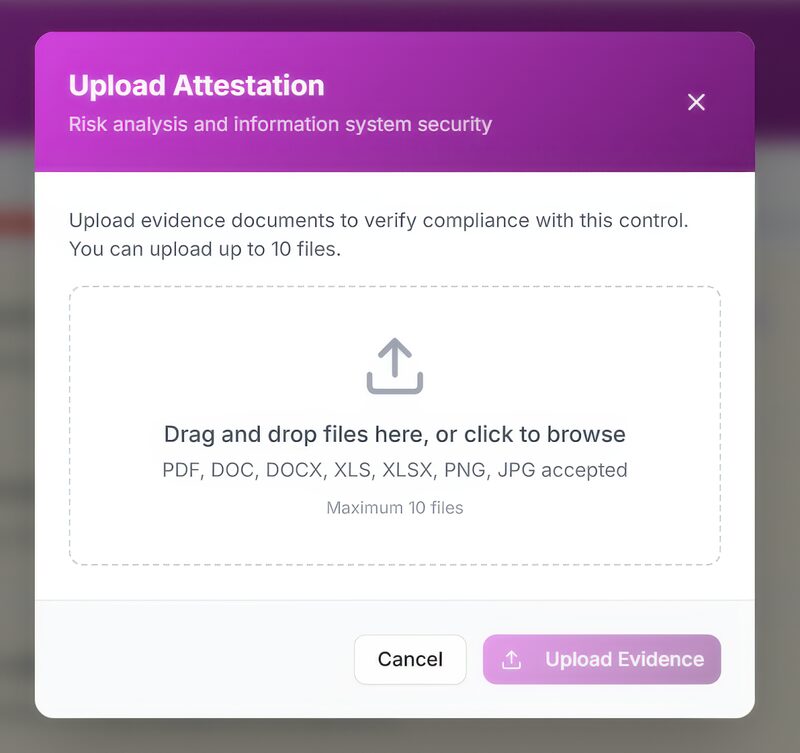
CYFAX auto-verifies 40–50% of controls through external reconnaissance alone. Add the optional PREVENT endpoint agent and auto-verification reaches 85%+ by validating internal controls against CIS Benchmarks and MITRE ATT&CK continuously. Remaining gaps are closed through the AI attestation engine, which reviews uploaded evidence documents for fitness-for-purpose against each regulatory requirement.
Six Capabilities. One Login. One Contract.
CYFAX Intelligence
External attack surface monitoring across 500B+ threat objects and 20,000+ criminal sources. Leaked credentials by name, exposed infrastructure, email security gaps, dark web mentions, and impersonation domains. 60-minute scan, zero install.
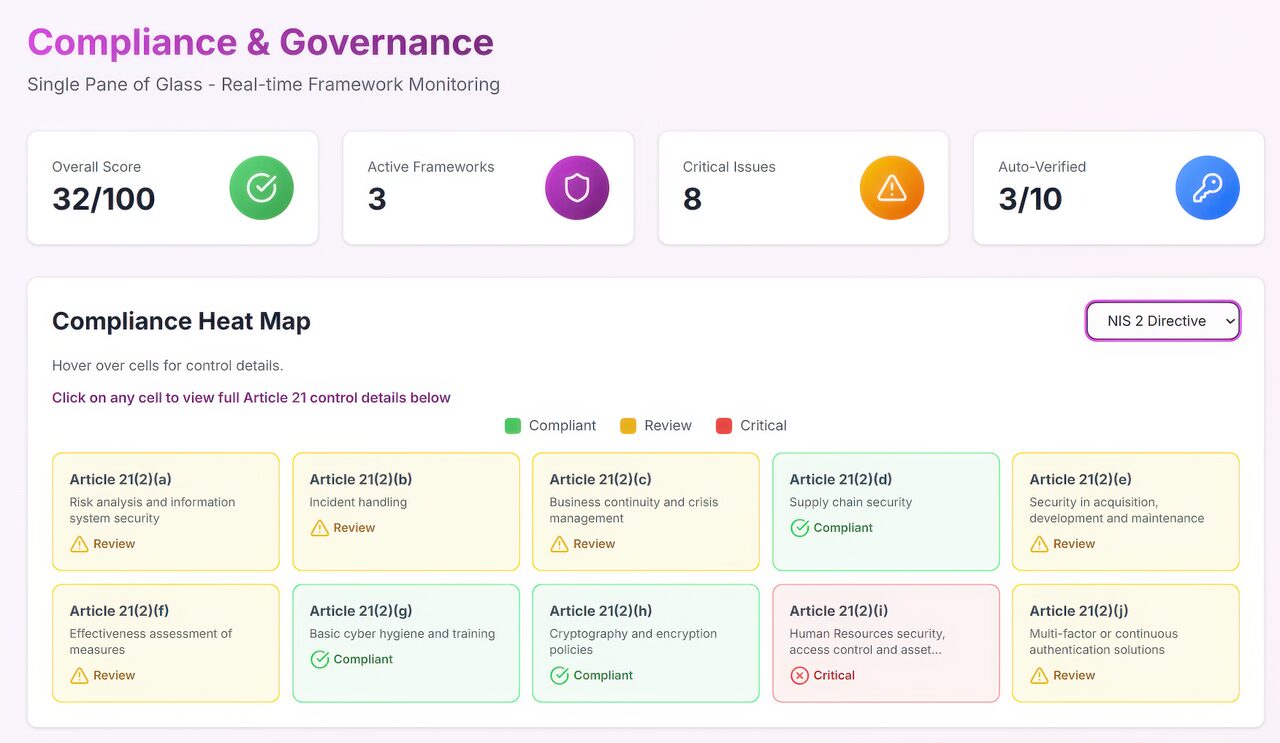
Compliance Cockpit
Real-time governance heatmap mapping controls to 350+ frameworks. AI reviews uploaded evidence for fitness-for-purpose. Framework dropdown selector for simultaneous multi-regulation view.
TPRM
Third-party risk management. Upload vendor domains via CSV, receive risk scorecards within hours. External exposures, credential status, email vulnerabilities — per vendor. Continuous monitoring with alerts.
ARETE Predictive AI
Breach probability modeling with 6–21 week prediction horizon. 3,600+ profiled threat actors scored against your specific environment. Forward-looking breach probability — not just risk scores.
VIP Monitoring
Dark web surveillance for named individuals — executives, partners, HNW clients. Credential leak monitoring, impersonation detection, criminal intent signals across 20,000+ underground sources.
PREVENT Agent
Lightweight endpoint agent. Deploys in ~10 min per VLAN. Validates 60+ internal controls, continuous BAS against CIS/MITRE, vulnerability scanning, NDR. Evidence feeds directly into Compliance Cockpit.
From Domain to Compliant in Days
Regulatory Compliance Guides
Detailed guides for specific regulatory frameworks. Each includes requirement mapping, CYFAX capability alignment, FAQ, and implementation guidance.